
European Digital Sovereignty and Telecommunications: From Regulator to Builder of Strategic Autonomy
Use this space to add a medium length description. Be brief and give enough information to earn with one click.
European Digital Sovereignty: The New Paradigm for the Telecommunications Sector
Digital sovereignty is not an end in itself, but is conceived as a fundamental piece within a much broader strategy that the European Union currently defines as the “Europe’s Independence Moment” or European Sovereignty.
The underlying idea is that Europe should be able to decide and act independently in key areas, without being overly dependent on external actors. In other words, to achieve full strategic autonomy that allows the EU to maintain its decision-making capacity in:
- Health and critical infrastructure
- Economy and trade
- Energy
- Defense and security
- Technology and data
The role of telecommunications in the European sovereignty strategy
In the current European context, telecommunications are a cross-cutting strategic infrastructure with multiple roles, such as:
- Critical infrastructure
- Enabler of the digital ecosystem
- Element of security and resillience
The traditional separation between digital technologies focused on data control, software, platforms and telecommunications focused on transmission operations and its physical capabilities, has been overcome in favor of a more integrated vision, especially since the emergence of technologies such as 5g/6G, edge computing and network virtualization.
Operators and regulators position telecommunications as ” infrastructure of sovereignty “: without strong networks there is no sovereign cloud, European AI or effective data protection.
What worries Europe from the perspective of its sovereignty?
Geopolitical context
Europe has entered a decisive phase that the Commission has dubbed the “Moment of Independence.” After decades of delegating its security to the US and its industrial growth to cheap energy and global supply chains, the current geopolitical context has forced an abrupt awakening. The concern is no longer merely regulatory; it is existential.
Defense: From Peace to “2030 Preparedness”
Geopolitical instability, marked by Russian aggression in Ukraine and escalating global tensions, has transformed defense into the top priority. Europe has come to accept that hybrid threats (cyberattacks, sabotage of critical infrastructure) do not distinguish between peace and war.
To address this, the EU has presented the White Paper on European Defence – “Readiness 2030 ”. This strategic document aims not only to revitalize the military industry but also to prepare civil society and critical infrastructure for conflict scenarios. The ReArm Europe Plan is the financial implementation arm of this strategy, seeking to mobilize massive investments to close urgent capability gaps.
Added to this is the Niinistö report , which underscores the need for integrated civil-military preparedness. The conclusion is clear: telecommunications, transportation, and energy are now dual defense assets. Without resilient networks, military mobility and crisis response are impossible.
The Dependency Trap: The US and China
The second major concern is technological autonomy. Europe depends on the United States and China for more than 80% of its critical technologies. This creates two fatal risks:
- Extraterritoriality and Espionage : The use of US cloud services and software exposes European companies and governments to laws such as the US Cloud Act or FISA , which allow foreign agencies to access data even if the servers are physically located in Europe. This creates a “sovereign prison”: local data, but foreign keys.
- Supply Chain Security : Reliance on high-risk suppliers (such as Huawei or ZTE) has been redefined as a national security threat, leading to their progressive exclusion from 5G and future 6G networks.
Economic Competitiveness: Draghi and Letta’s Diagnosis
Finally, the loss of economic relevance is a concern. Two key reports have defined the roadmap to avoid irrelevance:
- Draghi Report: Warns of an alarming innovation gap and a static industrial structure. Draghi estimates that €800 billion in annual investment is needed to maintain competitiveness, urging Europe to move from being a mere regulator to an active investor.
- Letta Report : Proposes adding a “Fifth Freedom” to the Single Market focused on research and innovation, integrating historically fragmented sectors such as telecommunications, energy and finance to gain scale.
Urgency of changing from Regulator to Builder
The response to these concerns crystallized at the Berlin Summit 2025 and the EuroStack initiative. Europe has decided to move beyond simply writing laws and begin building infrastructure. The objective is clear: to develop its own technology stack (cloud, AI, connectivity) and implement ” Buy European ” policies to ensure that public funds strengthen the continent’s real sovereignty.
Europe is no longer just looking to comply with rules; it is looking to survive and lead its own destiny.
A legal framework for evolving European technological sovereignty
Acceleration in the production of regulations related to technological sovereignty:
In the last two years, as much regulation has been generated as in the previous four years, highlighting the urgency of the EU’s sovereignty objectives.
| Acronym / Name | Official Legal Text | Year of Approval / Proposal | State / Year of Repeal |
|---|---|---|---|
| SAFE (SAFE) | Regulation (EU) 2025/2653 establishing Security Action for Europe. | 2025 | In force. |
| Quantum Act | Planned legislative initiative (Reference: Commission Work Programme). | Forecast Q2 2026 | Future proposal. |
| European Innovation Act | Planned legislative initiative. | Expected Q1 2026 | Future proposal. |
| ECCS (EUCCS) | Legislative initiative on critical communication system. | Forecast Q3 2026 | Future proposal. |
| 28th Regime | Legislative initiative for innovative companies | Expected Q1 2026 | Future proposal. |
| DNA | Proposed Regulation COM(2026) 16 (Digital Networks Act). | 2026 (Proposal) | Proposal to replace the CECE (Dir. 2018/1972). |
| CADA | Cloud and AI Development Act (Reference: Work Programme). | Expected Q1 2026 | Future proposal. |
| Defence Omnibus | Defence Mini-Omnibus Regulation | 2025 (Proposal) | Proposal. |
| Digital Omnibus | Proposal for Regulation COM(2025) 837 | 2025 (Proposal) | Proposal to repeal DGA (2022/868), Reg. 2018/1807 and Dir. 2019/1024. |
| CRA | Regulation (EU) 2024/2847 (Cyber Resilience Act). | 2024 | In force. |
| AI Act | Regulation (EU) 2024/1689 (Artificial Intelligence Regulation). | 2024 | In force. |
| eIDAS 2 | Regulation (EU) 2024/1183 (Amends Reg. 910/2014). | 2024 | In force (Amends eIDAS 1). |
| Data Act | Regulation (EU) 2023/2854 (Data Protection Act). | 2023 | In force. |
| Chips Act | Regulation (EU) 2023/1781 (Chip Act). [Source 1508] | 2023 | In force. |
| DGA | Regulation (EU) 2022/868 (Data Governance Act). | 2022 | in force (Proposed for its repeal by Digital Omnibus) |
| NIS2 | Directive (EU) 2022/2555 (Cybersecurity). | 2022 | Repeals NIS Directive 1 (2016/1148). |
| DORA | Regulation (EU) 2022/2554 (Digital Operational Resilience). | 2022 | In force. |
| CER | Directive (EU) 2022/2557 (Resilience of Critical Entities). | 2022 | Derogation from Directive 2008/114/EC. |
| DMA | Regulation (EU) 2022/1925 (Digital Markets). | 2022 | In force. |
| DSA | Regulation (EU) 2022/2065 (Digital Services). | 2022 | In force. |
| ENS | Royal Decree 311/2022 (National Security Scheme – Spain). | 2022 | Repeals Royal Decree 3/2010 |
| Cyber-Act | Regulation (EU) 2019/881 (Cybersecurity Act). | 2019 | In force (proposed for repeal by “Cybersecurity Act2”) |
| CECE | Directive (EU) 2018/1972 (European Electronic Communications Code). | 2018 | In force (Proposed replacement by DNA). |
| GDPR | Regulation (EU) 2016/679 (General Data Protection Regulation). | 2016 | Derogation from Directive 95/46/EC |
| NIS | Directive (EU) 2016/1148 (NIS 1). | 2016 | Repealed by NIS2 (Dir. 2022/2555). |
Key laws for telecommunications sovereignty
The complex legal framework linked to the European sovereignty strategy has numerous interactions among its regulations that, to a greater or lesser extent, can affect any technology. However, if we have to focus on a shortlist of regulations that particularly affect the telecommunications sector, I would pay special attention to:
- DORA and NIS2 : Regulations that already penalize the concentration of risk in a single foreign provider, forcing companies to diversify their technology stack with European alternatives.
- Digital Networks Act (DNA): Integrate the European market so that local operators can gain scale and accelerate the deployment of Full-Fiber and ubiquitous 5G.
- Cybersecurity Act (CSA2 revision) : Introduces the physical exclusion of “high-risk” suppliers (such as Huawei or ZTE) from critical infrastructure within a maximum period of 36 months.
- Cyber Resilience Act (CRA) : Establishes that all digital products must be “secure by design” and requires manufacturers to manage vulnerabilities throughout their lifecycle.
From recommendations (soft law) to obligations (hard law)
In the context of European digital sovereignty, a fundamental structural change has taken place: the European Union has abandoned the “soft law” approach (recommendations and directives with a wide margin of national discretion) to adopt a “hard law” framework (Directly applicable Regulations and Directives of maximum harmonisation).
The main regulations that have transformed recommendations or voluntary approaches into strict legal obligations are:
1. From discretion to obligation in Cybersecurity (NIS1 → NIS2)
The most obvious transformation is in the security of networks and information systems.
- Previously (NIS1 Directive): Member States had discretion to identify which companies were “operators of essential services.” This led to fragmentation, as a company could be considered essential in one country but not in another.
- Now (NIS2 Directive): State discretion is eliminated. The “size-cap rule” is introduced, which automatically designates all medium and large companies in critical sectors (energy, transport, banking, digital infrastructure, etc.) as regulated entities (essential or important), obligating them to comply with risk management and incident reporting requirements. Furthermore, senior management responsibility shifts from a recommendation of best practices to a legal obligation with personal penalties.
2. From voluntary security to “Safety by Design” (SBD)
- Previously: There was no horizontal EU framework. The cybersecurity of hardware and software products depended on the manufacturer’s discretion or on fragmented national regulations.
- Now (Cyber Resilience Directive – CRA) : It is now mandatory for all products with digital components (from smart toys to industrial firewalls) to meet essential cybersecurity requirements in order to obtain CE marking. Without this mandatory compliance, the product cannot enter the European market. It is also mandatory to guarantee security updates throughout the product’s lifespan.
3. From voluntary notification to the Mandatory Identity Wallet (eIDAS → eIDAS 2)
- Previously (eIDAS 1): Member States could voluntarily notify their electronic identification systems for cross-border recognition, but were not obliged to issue a digital identity to their citizens.
- Now (eIDAS Regulation 2) : All Member States are obliged to provide a European Digital Identity Wallet (EUDI Wallet) to their citizens by 2026. In addition, major platforms and essential services are obliged to accept this wallet as a method of authentication.
4. From supervisory guidelines to Direct Financial Regulation (DORA)
- Previously : ICT risk management in the financial sector was based on guidelines from European Supervisory Authorities and disparate national regulations.
- Now (DORA Regulation) : These rules are consolidated into a directly applicable regulation that obliges financial institutions to manage third-party risk (ICT providers). DORA empowers regulators to directly monitor critical technology providers (such as large cloud providers), something that was previously outside their direct jurisdiction.
5. From the “Toolbox” to the exclusion of suppliers (5G Toolbox)
- Previously: The “5G Cybersecurity Toolbox” was a set of recommendations to mitigate risks in networks, suggesting restrictions on high-risk providers.
- Now (Economic Security Strategy and DNA): Implementation is becoming more stringent and mandatory. New legislative proposals and revisions (such as the revised Cybersecurity Act) seek to impose strict deadlines (e.g., 36 months) for the mandatory removal of equipment from “high-risk” vendors (such as Huawei or ZTE) from critical parts of telecommunications networks, shifting from a security recommendation to a national security and sovereignty imperative.
6. From voluntary to mandatory certification (Cybersecurity Act)
The Cybersecurity Act (CSA) stipulates that European certification schemes are voluntary, unless otherwise specified by Union or Member State law. However, recent legislation has created avenues for making them mandatory.
- Previously : The EU cybersecurity certification framework was, by default, voluntary for manufacturers who wanted to demonstrate the security of their products.
- Now : Through the amendments introduced by the CRA and the revision of the Cybersecurity Act (CSA), the Commission now has the power to adopt delegated acts to make European certification mandatory for product categories considered “critical” or “high risk”.
ECCF (European Cybersecurity Certification Framework)
The ECCF (European Cybersecurity Certification Framework) is a regulatory system established by the European Union to create harmonised certification schemes at the continental level for Information and Communication Technology (ICT) products, services and processes.
The ECCF is not a single certification, but rather an umbrella under which specific schemes are developed for different technologies. ENISA (the EU Agency for Cybersecurity) is responsible for preparing these schemes. Some examples:
- EUCC (Common Criteria) : For ICT products (hardware, software, chips, smart cards). It was the first scheme adopted (Implementing Regulation (EU) 2024/482).
- EUCS (Cloud Services) : Scheme for cloud services (SaaS, PaaS, IaaS). It has faced political challenges related to data sovereignty requirements.
- EU5G : For 5G networks.
- EUMSS (EU Cybersecurity Certification Scheme for Managed Security Services) : It is the scheme designed to certify managed security service providers (MSSPs).
- EUDI Wallets (Certification for EU Digital Identity Wallets) : For mobile digital identity.
- EUIA (EU Artificial Intelligence Cybersecurity Scheme – proposal) : For AI systems.
Its original legal basis is the Cybersecurity Act (CSA) 2019 (Regulation (EU) 2019/881). The ECCF was initially designed as a voluntary framework. However, the regulations are evolving towards mandatory implementation in critical cases. Due to the slow implementation of some schemes, the Commission has proposed a revision of the regulation (known as Cybersecurity Act 2 or CSA2), which is expected to be part of the regulatory package by 2026.
The new features that this reform will introduce for the ECCF include:
- Cyber Posture Certification: This will allow the certification not only of a product, but also the security management of an entire entity or organization, facilitating compliance with directives such as NIS2.
- Managed Security Services : The scope is expanded to include the certification of managed security service providers (MSSPs), such as those that perform incident response or audits.
- Simplification: Seeks to streamline the development of schemes (with a target timeframe of 12 months).
Mandatory CE marking in cybersecurity
The CE marking is the mandatory mark known to all Europeans, which indicates that a product complies with all the safety, health and environmental protection regulations of the European Union in order to be marketed in the Single Market.
Historically, for telecommunications equipment, CE marking focused on electrical safety and electromagnetic compatibility (RED Directive). However, with the new Cyber Resilience Act (CRA), cybersecurity has become an essential requirement for obtaining this marking.
It guarantees that the product has been designed, developed and produced with security (Security by Design), has no known exploitable vulnerabilities at the time of its release and that the manufacturer guarantees security updates throughout its useful life.
For products classified as “Important” (Class I and II) or “Critical”, the law normally requires a conformity assessment carried out by an external auditor (notified body).
It must be placed visibly, legibly, and indelibly on the product (or on its packaging/documentation if that’s not possible). For software, it can be on the declaration of conformity or on the website.
The CE Marking is the mandatory “gateway”: No product with digital elements (such as an SBC or a router) will be able to be sold in the EU without it from the full application of the CRA (December 2027).
Interactions of ECCF and AI Act with CE Marking
If a product obtains certification under an ECCF scheme (e.g., the EUCC), it is automatically presumed to meet the cybersecurity requirements necessary for CE marking within the CRA scope.
The European Commission has the power to require critical (highly sensitive) product categories to obtain mandatory European certification under the ECCF in order to bear the CE marking and enter the market. In these cases, the CE marking is entirely dependent on the ECCF.
The AI Act is not an ECCF scheme, although there is already an equivalent proposal for its development (EUIA). The AI Act is a horizontal product safety regulation (like those governing elevators or toys). It has its own pathway for obtaining CE Marking based on “Essential Requirements.”
If a telecommunications product integrates AI, it must have two declarations of conformity: one imposed by the ECCF and the other by the AI Act (related to trust, data ethics, etc.). On paper, you might meet the cybersecurity criteria certified by the ECCF framework, but not comply with the AI Act, and therefore you wouldn’t be able to mark your product with the CE marking.

Key initiatives for telecommunications sovereignty
Civil Infrastructure as a Basis for Military Capability (Dual Use)
Civilian infrastructure must be battle-ready to support military deterrence, requiring private operators to assume national security responsibilities. This obliges operators (and other essential entities) to meet military security standards, diversify their suppliers (de-risking) to avoid geopolitical dependencies, and actively participate in EU-funded dual-use infrastructure projects.
The telecommunications sector is perhaps where this concept of “dual use” is most transformative. Civilian networks are no longer seen solely as public services, but as strategic defense assets.
EUCCS : The EU Critical Communications System (EUCCS) is being created to connect emergency and security services across borders, removing the geopolitical limitations of current networks.
5G and the Battlefield : 5G networks are considered the “backbone” for essential domestic market services, but they are also key to “defense readiness.” They enable the ultra-fast connectivity needed for real-time data exchange, drone detection, and battlefield coordination.
Obligations for Operators : As highlighted in the presentation slides, this approach obliges telecom operators (and other essential entities) to comply with military security standards, diversify their suppliers to avoid geopolitical dependencies (such as de-risking high-risk suppliers like Huawei/ZTE) and actively participate in EU-funded infrastructure projects for dual use.
Strategic shift from Regulator to Builder: EuroStack Initiative and the Berlin Summit 2025
German Chancellor Merz presented EuroStack as a strategic framework to reduce dependence on foreign hyperscalers by fostering European alternatives in AI, cloud and cybersecurity.
The focus is on the ownership of the infrastructure (physical and logical), which translates into moving from rhetoric to a real investment strategy, to secure the foundational layers of the digital economy against geopolitical shocks.
The role of “Builder” implies that the EU and Member States must cease being mere observers of the market and intervene directly in the creation of industrial capacity:
- Physical and Logical Infrastructure: Ownership of the infrastructure is being sought. This includes initiatives such as the Digital Commons EDIC (European Digital Infrastructure Consortium) to create open alternatives to proprietary platforms.
- Public and Private Investment: The need to mobilize massive capital is highlighted, exemplified by investments such as Schwarz Digits (11 billion euros) or the SAP-Mistral partnership, aligned with this political vision.
- Public Procurement (“Buy European”): The shift to “builder” means using the purchasing power of the public sector to create guaranteed markets for sovereign and open-source technologies, rather than providing temporary subsidies. It ensures that European taxpayer money is reinvested in strengthening the local industrial and technological base, instead of subsidizing foreign competitors who already dominate the market.
Strict definition of a European company
The main motivation behind the creation of a “strict definition of a European company” —driven primarily by the EuroStack initiative and the European private sector— is to avoid “Euro-washing” and ensure real sovereignty that goes beyond simply localizing data.
- Control: The majority of voting control must be in the hands of European entities or individuals (“absence of non-EU control”).
- Jurisdiction: Legal headquarters and main tax domicile in Europe, paying most of its corporate taxes on the continent.
- Local R&D: Most research and development activity should be carried out in Europe.
- Without extraterritorial restrictions: The technology should not be subject to intellectual property licenses or export controls from third countries (such as the US Cloud Act).
Measuring real sovereignty: SEAL (Sovereignty Effectiveness Assurance Levels)
Although SEALs are not legally mandated, the levels they establish and their equivalent measures are part of the procurement processes of various government agencies. They act as a de facto standard for public tenders, even though they are not explicitly mentioned. It is highly likely that a future legislative review will eventually enshrine them in law.
The origin of SEAL (Sovereignty Effectiveness Assurance Levels) is found in the European Commission, specifically within the EU Cloud Sovereignty Framework, whose final and operational version was consolidated between the end of 2024 and 2025.
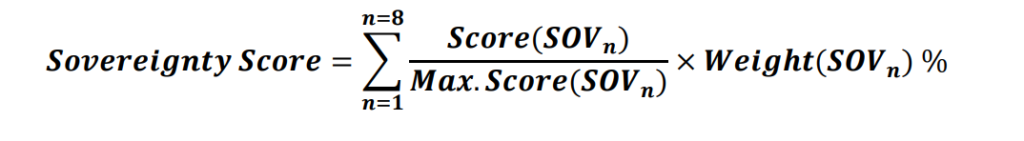
This model arises from the Commission’s need to have an objective “measuring stick” for its own tenders (such as the Cloud III purchasing system) and to avoid so-called sovereignty washing (when a supplier claims to be sovereign just because it has servers in Europe, but its real control resides in the US or China).
